Application Security , Blockchain & Cryptocurrency , Cryptocurrency Fraud
Hackers Abuse Remote Access Tools to Steal Crypto Data
Bad Actors Use SpyAgent Malware, Deploy Social Engineering to Lure Victims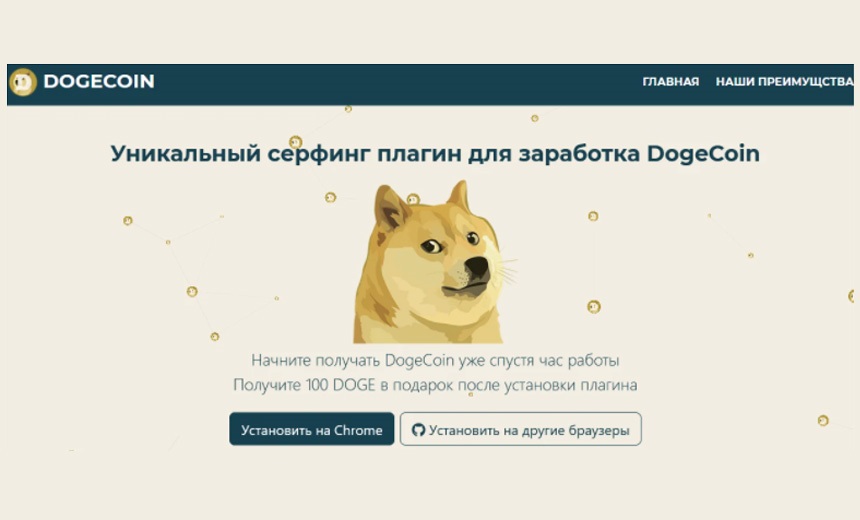
Unidentified threat actors have launched a campaign to using fake cryptocurrency-related websites distribute the SpyAgent malware, which abuses legitimate remote access tools, such as TeamViewer.
See Also: Ransomware Response Essential: Fixing Initial Access Vector
A new version of the malware has been targeting a legitimate Russian remote access tool called Safib Assistant, according to researchers at cybersecurity firm Trend Micro.
The financially motivated threat actors seek to steal credentials and cryptocurrency wallets, and replace cryptocurrency addresses shared via a clipboard, the researchers note.
The updated variant of SpyAgent involves the exploit of a Dynamic Link Library, or DLL, sideloading vulnerability, which causes a malicious DLL to load, the researchers say. This, in turn, "hooks and patches" various API functions called by the remote access tool and ultimately hides the remote access tool window from the user.
"The malicious DLL then begins reporting the remote access tool's ID, which the malware operator needs to connect to and control the infected machine. The malware sets the access password to a fixed one, so that merely knowing the remote access tool's ID is enough for the attacker to successfully connect to the infected machine," says Jaromir Horejsi, senior cyberthreat researcher at Trend Micro.
SpyAgent also downloads other malware to perform additional tasks, such as stealing data, the researchers say. They also report that SpyAgent uses commodity stealers, such as RedLine, Ducky, AZORult, Cypress and Clipper. Clipper is a clipboard replacer that replaces various cryptocurrency addresses with those controlled by the malicious actor, they add.
The campaign also uses remote access Trojans such as Remcos RAT, NanoCore, njRAT and AsyncRAT, the researchers say.
Initial Attack Vector
SpyAgent's malware dropper is distributed using fake cryptocurrency-related websites in the Russian language, the researchers say. This dropper, they add, poses as a fake cryptocurrency wallet, miner or surfing plug-in.
The researchers note that the threat actors use social engineering techniques, such as running "earn cryptocurrency for browsing" advertisements, to direct victims to the fake websites. Horejsi adds that not "all websites offering cryptocurrency in exchange for views are necessarily malicious."
When users visit one of the fake websites, they are prompted to save and run an executable file, Horejsi says.
"Due to search engine optimization, simply searching for the right keywords might result in the inclusion of these websites in search results," the researchers note.
The threat actors have also leveraged social media platforms, such as Twitter, as infection vectors, the researchers say. In one case, the researchers spotted a legitimate-looking Twitter account, which they suspected to have been compromised. They did not disclose the account's identity.
Technical Details
Horejsi notes that the dropper is created using the Nullsoft Scriptable Install System, or NSIS, installer - a tool for creating scriptable program installers.
The dropper file contains one randomly named encrypted binary file that calls for Microsoft CryptoAPIs to decrypt this file, which gives a 7-Zip archive that extracts several files that includes legitimate non-malicious files belonging to the remote access tools.
The extracted file includes a batch file (.bat), which starts the main executable (Assistant, ast.exe) file. The Config file (.cfg) contains encrypted configuration and the bitmap file (.bmp) is used for deriving the key to decrypt the config file.
"The quartz.dll is the malicious DLL containing the malware that is sideloaded by ast.exe. Although the real length of the quartz DLL is several dozens of kilobytes, its length is artificially inflated by appending a huge overlay of zeroes. This is likely to prevent or discourage some security solutions from uploading these large files for further analysis," the researchers note.
Once the decryption is done, the configuration file contains the URL address of the command-and-control server, where the domain part is used as a key for another decryption, this time as part of where the DLL’s executable code resides since a portion of the DLL is a self-modifying code.
"The first decrypted function is responsible for resolving the API function addresses, while the second decrypted function is responsible for hooking various functions and altering the default behavior of the remote access tools," the researchers say.
Mitigation
Defending against this attack is straightforward, according to the researchers. As the malicious actors leverage "traditional social engineering techniques, such as fake websites, malicious advertisements, and spurious social media posts, users are recommended to practice due diligence and avoid selecting any suspicious links or visiting dubious websites," they say.
"We also encourage users to perform security best practices such as bookmarking trusted sites and practicing caution when visiting new websites, especially those that are prone to being abused for social engineering attacks," Horejsi notes.
"The focus should be on staff awareness and logical controls," says Ron Williams, a PCI QSA consultant at IT Governance Ltd.
Williams recommends that security leaders limit administrative access to specific user accounts, keep up to date with the latest patches offered by vendors and train their staff on how attackers are likely to compromise them.