Cybercrime , Cybercrime as-a-service , Cyberwarfare / Nation-State Attacks
US Prosecutors Charge Latvian Woman in Trickbot Gang Case
Case Is First Test for DOJ's Ransomware and Digital Extortion Task Force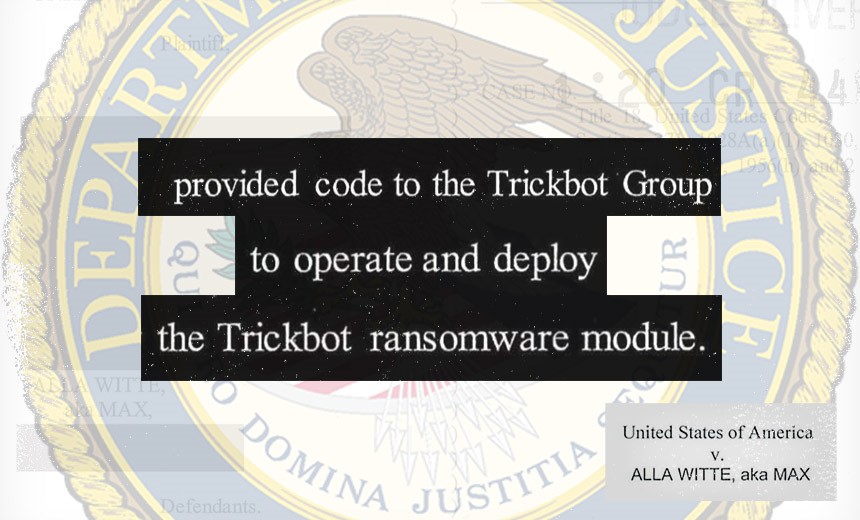
A 55-year-old Latvian woman has been charged with helping to develop code for the Trickbot cybercriminal gang as well as allegedly stealing banking credentials from victims around the world and helping to distribute ransomware through the botnet the group created, according to the U.S. Justice Department.
See Also: Ransomware Response Essential: Fixing Initial Access Vector
Alla Witte, who also went by the online handle "Max," faces 19 criminal charges, including conspiracy to commit computer fraud and aggravated identity theft, conspiracy to commit wire and bank fraud affecting a financial institution, bank fraud affecting a financial institution, aggravated identity theft and conspiracy to commit money laundering, according to the federal indictment unsealed Friday.
The most serious charges, conspiracy to commit wire and bank fraud and substantive bank fraud, each carry a possible 30-year prison term, according to the Justice Department.
The case against Witte is one of the first to be brought by the Justice Department's Ransomware and Digital Extortion Task Force, which was created in April to tackle ransomware and extortion attempts and prosecute cases in a more systematic fashion.
Witte, who was born in Russia, was arrested by the FBI in February and has been held in federal custody since then. On Friday, her case was transferred to the U.S. Attorney's Office for the Northern District of Ohio, which is overseeing the prosecution, according to federal authorities, and the Justice Department unsealed the 47-count indictment against her.
Trickbot
The federal case involving Witte is one of the first to target an alleged member of the Trickbot group, which has been active since at least 2015. The gang has used the malware for a variety of purposes over the years, including deploying it as a banking Trojan and then creating a botnet with which the malicious code could be used to distribute ransomware to a wide variety of victims, including hospitals, schools, public utilities and government agencies as well as private companies and individuals, according to the Justice Department (see: Emotet, Ryuk, TrickBot: 'Loader-Ransomware-Banker Trifecta').
In October 2020, Microsoft, several U.S. government agencies and other security firms worked to take down Trickbot's infrastructure just before the November elections. By January, however, researchers and analysts had seen signs of the botnet returning to life (see: Is Trickbot Botnet Making a Comeback?).
Ransomware Task Force
"These charges serve as a warning to would-be cybercriminals that the Department of Justice, through the Ransomware and Digital Extortion Task Force and alongside our partners, will use all the tools at our disposal to disrupt the cybercriminal ecosystem," says Deputy Attorney General Lisa Monaco.
Last week, the Justice Department issued new guidance for prosecutors, to ensure that all cases they're tracking - domestically and abroad - get coordinated with the task force, and the White House has urged business to do more to harden their infrastructure against these types of attacks (see: White House Urges Businesses: Improve Ransomware Defenses).
On Friday, White House press secretary Jen Psaki noted again that ransomware and the cybercriminal gangs behind these attacks will be topic of discussion when President Jose Biden meets with Russian President Vladimir Putin in Switzerland on June 16.
"[Biden] also will raise cyber activity, malign activity, problematic activity and the harmful activity we've seen take place. Of course, there is the SolarWinds hack, but also the ransomware hacks," Psaki said. "As we've talked about, the actions of criminal groups within a country - there’s a responsibility of the leaders of that country to take action. And there's no doubt President Biden will be raising that directly in that conversation."
Trickbot Gang
The 47-count indictment unsealed Friday offers an in-depth look at how the Trickbot gang developed into a criminal organization since 2015, including how one member of the group obtained the credentials to a private server used by the operators of the Dyre malware. After Russian police disrupted the Dyre operation, some members began using some of that code to create a new malware framework and operation that would eventually become Trickbot, according to federal prosecutors.
The federal indictment charging Witte with multiple criminal charges is heavily redacted in several places, with the names of several alleged members of the gang blacked out, which would indicate that the FBI and federal prosecutors know their identities.
During her time with the Trickbot gang, Witte allegedly worked as a malware developer for the group and wrote code related to the control and deployment of ransomware and payments of ransoms, according to federal prosecutors.
For example, federal prosecutors allege that Witte helped develop a web panel that operated the Trickbot ransomware module and included separate panels for "'targets," ''bots" and "users" of the ransomware. It also contained code that automatically doubled ransom amounts if a victim did not pay within a period determined by the Trickbot Group.
"A web page used to inform victims that their computer was encrypted with ransomware and to provide a bitcoin address used by Trickbot Group to obtain a ransom payment," according to the indictment. "The web page included the following language: 'Your computer has been infected! Your documents, photos, databases and other important files [are] encrypted. To decrypt your [files] you need to buy our special software.'"
Alleged Theft
Besides the ransomware operations, the indictment alleges Witte and others used the Trickbot malware to steal money and personal data from victims around the world, including the U.S., the U.K. Australia, Belgium, Canada, Germany, India, Italy, Mexico, Spain and Russia.
Witte and other members of the gang allegedly deployed Trickbot to capture online banking credentials, credit card numbers, email addresses, passwords, dates of birth, Social Security numbers and addresses. Witte and others also stole credentials and personal data to access online bank accounts to transfer electronic funds and launder money throughout U.S. and foreign bank accounts.
"Witte provided code to the Trickbot Group for a web panel used to access victim data stored in a database. The database contained a large number of credit card numbers and stolen credentials from the Trickbot botnet," according to the indictment.